At CERRIX, we like to say that we don’t just build a GRC platform, we live in it.
Our own Information Security Management System (ISMS) runs entirely on CERRIX GRC, the same software our clients use every day. It’s how we manage risks, execute controls, handle incidents, and prepare for ISO 27001 audits.
For us, it’s not about ticking compliance boxes. It’s about creating trust, inside the company and with everyone we work with.
Why We Built Our ISMS in CERRIX GRC
When we started designing our ISMS, the goal wasn’t just to meet certification requirements. We wanted to embed information security into how we work every day.
That meant three things: full visibility, clear accountability, and continuous improvement.
CERRIX GRC gave us exactly that. Every risk, policy, and control is connected. We can instantly see how effective our measures are and where improvements are needed. What used to live in spreadsheets and shared folders now lives in one clear, central place.
As one of our colleagues put it:
“Our ISMS gives us a clear picture of how we’re doing on information security. We can show what’s under control and what still needs work, all with one click.”
That clarity turned compliance into confidence.
New to ISMS? Read our primer: What Is an ISMS? A Practical Guide for Risk & Compliance Leaders in 2025
Centralized Control Execution and Monitoring
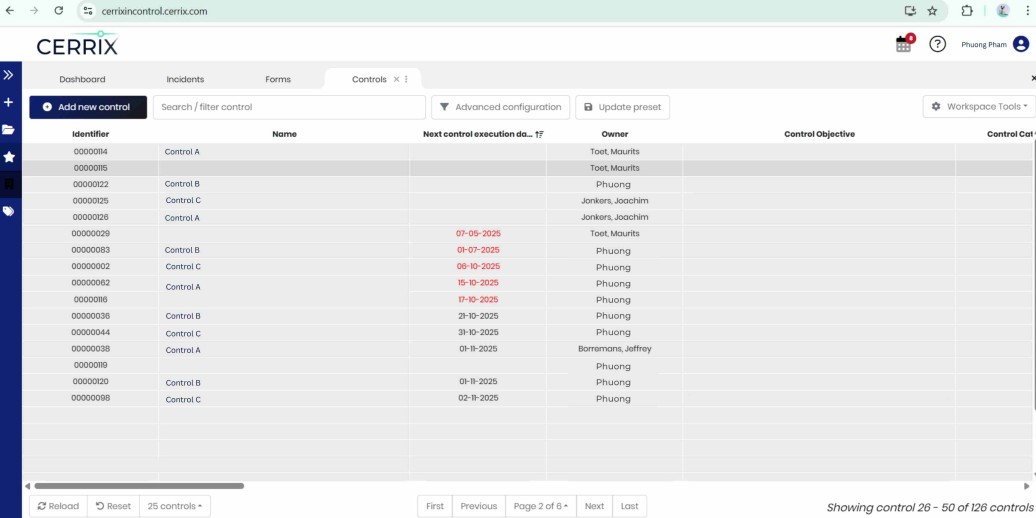
Within the Controls Module, every security control in our ISMS is treated as an actionable task.
This allows our information security team to plan, execute, and monitor control activities in a structured way.
Each control has a responsible owner, frequency, and review date. Automated reminders ensure nothing slips through the cracks, and monthly ISMS status reports are generated directly from CERRIX GRC, showing which controls are active, overdue, or pending review.
All evidence is stored within the same environment. This makes audits seamless. Auditors can access historical data and evidence instantly, without endless file searching or email trails.
Over time, this rhythm has created a healthy routine. Controls are not just tasks on a list; they are commitments that drive how we stay in control.
Managing Incidents and Continuous Improvement
Incident management plays a key role in our ISMS.
Any event, from a phishing attempt to a technical error, is logged as an Incident in CERRIX GRC Tool. Each incident is categorized by risk level, evaluated for impact, and linked to a Measure of Improvement (MOI) where necessary.
This creates a closed feedback loop. Incidents trigger corrective actions, and MOIs ensure follow-up until the issue is resolved.
That cycle of detect, act, and improve is what keeps our ISMS evolving. It’s also one of the core principles of ISO 27001: continuous improvement.
Policies, Risks, and Controls All Connected
All our key policies, such as the Information Security Policy, Code of Conduct, and Business Continuity Plan, are documented and maintained in the CERRIX GRC Software.
Each year, employees confirm they have read and understood these policies through Forms, providing a verifiable audit trail.
Because policies, risks, and controls are linked in the platform, we can clearly see how policy objectives translate into daily operations.
For instance, if a policy requires encryption of data or restricted access, the related controls, risk assessments, and test results are connected. This makes it easy to demonstrate compliance and identify areas for improvement.
This linkage is what makes our ISMS more than documentation; it’s a living system that shows how governance works in practice.
Visibility Through Dashboards and KPI Monitoring
The ISMS is monitored through dashboards that visualize the status of risks, controls, and incidents.
For management reporting, CERRIX GRC connects seamlessly with Power BI, allowing us to track key metrics such as:
- Control completion rate
- Number and severity of incidents
- Status of open MOIs
- Risk trends over time
These insights make it easy for leadership to stay informed, spot patterns, and make data-driven decisions.
It also helps us see progress over time, how our controls perform, how quickly incidents are resolved, and how we are improving as an organization.
This kind of visibility turns data into direction.
Always Ready for the Audit
Before we moved to CERRIX GRC, audit preparation meant collecting files and evidence weeks in advance.
Now, it’s a simple review process. Every control is mapped to its corresponding ISO 27001 clause, every update is logged automatically, and all documentation is connected.
We don’t prepare for audits once a year anymore. We stay ready all year round.
A System That Improves Itself
Running our ISMS on CERRIX GRC also helps us improve the software itself.
We see what works, what could be smoother, and what would make things easier for our users. Those ideas go straight into our product roadmap.
It’s one of the best ways we can test and refine our platform, by using it ourselves every day.
That’s why, when we tell clients that CERRIX GRC helps them stay in control, we mean it literally.
What We’ve Learned
Our ISMS journey taught us that good governance is about people and clarity as much as technology.
When everyone knows their responsibilities, when the process is transparent, and when insights are easy to access, security becomes part of the culture rather than a compliance exercise.
That’s what CERRIX GRC has given us, not just compliance but confidence.
Practicing What We Preach
Using CERRIX GRC to manage our ISMS keeps us grounded.
It means we don’t just advise others on governance and compliance; we practice it every day.
And every time we improve something internally, the platform gets stronger for our clients too.
That’s what "in control, by design" truly means.
Curious how this works in practice? Request a demo.

%20(1).jpg)
.avif)




.jpg)
%20(1).png)
.jpg)
%20(3).jpg)

.jpg)
.jpg)
.jpg)
.jpg)
.jpg)
%20(1).jpg)
.jpg)
%20(1).jpg)
.jpg)
.jpg)

.jpg)
.jpg)





.jpg)

%20(2).jpg)
















%20(1)%20(2).jpg)





.jpg)

.png)
.jpg)






%20(1).avif)



